5.7 KiB
sidebar_position
| sidebar_position |
|---|
| 1 |
Deploy AWX on RKE2 Cluster
Deploying a Rancher RKE2 Cluster based Ansible AWX server may be considered overkill for a homelab, however the configuration seen below allows you to scale the needs of the cluster over time and gives you more experience with a more enterprise-ready cluster.
 :::note Prerequisites
This document assumes you are running Ubuntu Server 20.04 or later with at least 8GB of memory and 4 CPU cores.
:::
:::note Prerequisites
This document assumes you are running Ubuntu Server 20.04 or later with at least 8GB of memory and 4 CPU cores.
:::
Deploy Rancher RKE2 Cluster
You will need to follow the Rancher RKE2 Cluster Deployment guide in order to initially set up the cluster itself. After this phase, you can focus on the Ansible AWX-specific aspects of the deployment. If you are only deploying AWX in a small environment, a single ControlPlane node is all you need to set up AWX. :::tip
If this is a virtual machine, after deploying the RKE2 cluster and validating it functions, now would be the best time to take a checkpoint / snapshot of the VM before moving forward, in case you need to perform rollbacks of the server(s) if you accidentally misconfigure something. :::
Server Configuration
The AWX deployment will consist of 3 yaml files that configure the containers for AWX as well as the NGINX ingress networking-side of things. You will need all of them in the same folder for the deployment to be successful. For the purpose of this example, we will put all of them into a folder located at /awx.
Make the deployment folder
mkdir -p /awx
cd /awx
Run a command to adjust open file limits in Ubuntu Server (just-in-case)
ulimit -n 4096
Create the AWX deployment configuration files
You will need to create these files all in the same directory using the content of the examples below. Be sure to replace values such as the spec.host=ansible.cyberstrawberry.net in the awx-ingress.yml file to a hostname you can point a DNS server / record to.
apiVersion: kustomize.config.k8s.io/v1beta1
kind: Kustomization
resources:
- github.com/ansible/awx-operator/config/default?ref=2.4.0
- awx.yml
- awx-ingress.yml
images:
- name: quay.io/ansible/awx-operator
newTag: 2.4.0
namespace: awx
apiVersion: awx.ansible.com/v1beta1
kind: AWX
metadata:
name: awx
spec:
service_type: ClusterIP
apiVersion: networking.k8s.io/v1
kind: Ingress
metadata:
name: awx-ingress
spec:
rules:
- host: ansible.cyberstrawberry.net
http:
paths:
- pathType: Prefix
path: "/"
backend:
service:
name: awx-service
port:
number: 80
Deploy AWX using Kustomize
Now it is time to tell Rancher / Kubernetes to read the configuration files using Kustomize (built-in to newer versions of Kubernetes) to deploy AWX into the cluster. Be sure that you are still in the /awx folder before running this command. **Be Patient: ** The AWX deployment process can take a while. Go grab a cup of coffee and use the commands in the Troubleshooting
section if you want to track the progress more directly.
kubectl apply -k .
:::caution
If you get any errors mentioning "CRD" in the output, re-run the kubectl apply -k . command a second time after waiting about 10 seconds. The second time the error should be gone.
:::
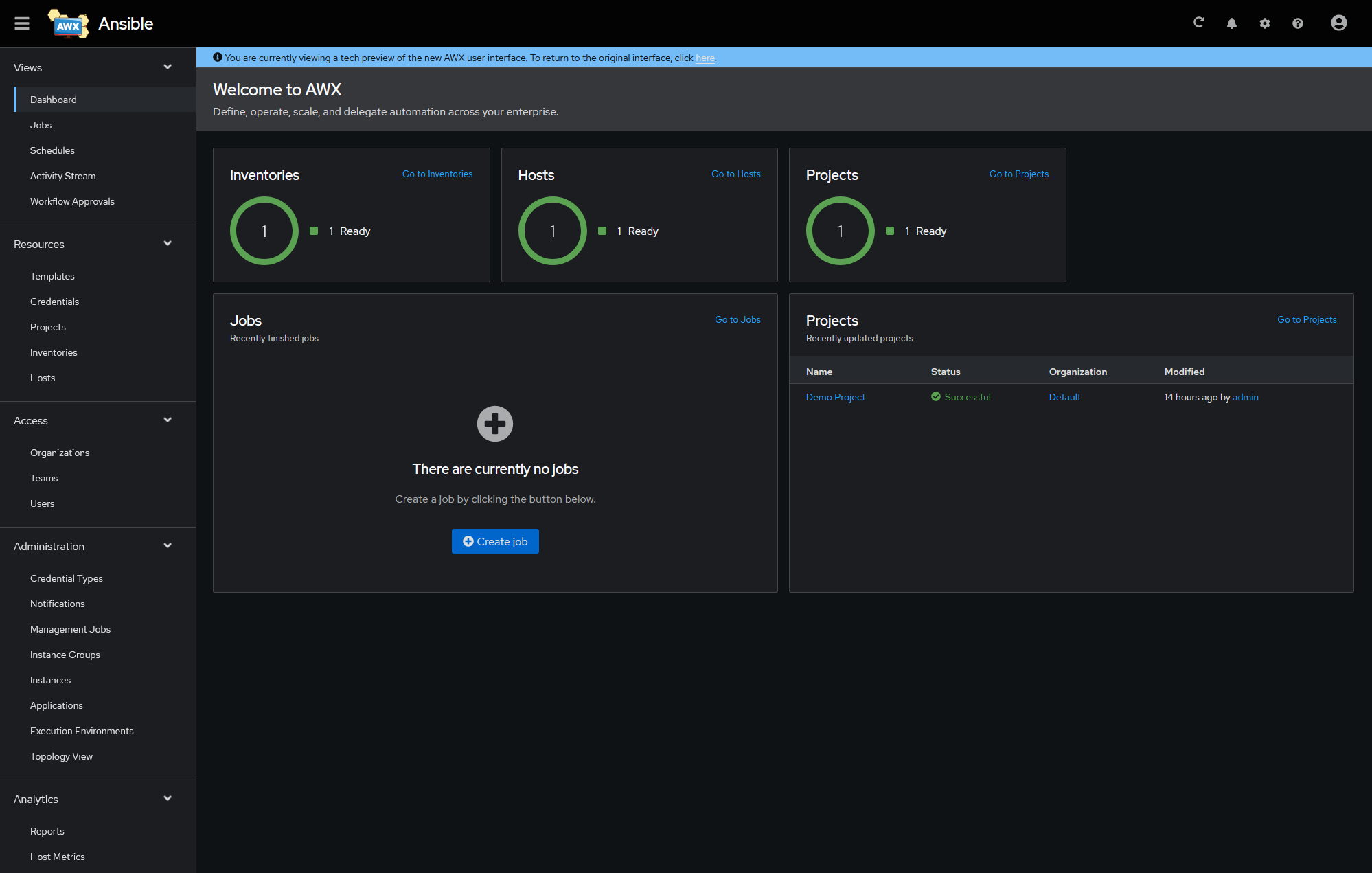
Access the WebUI behind Ingress Controller
After you have deployed AWX into the cluster, it will not be immediately accessible to the host's network (such as your home computer) unless you set up a DNS record pointing to it. In the example above, you would have an A or CNAME DNS record pointing to the internal IP address of the Rancher RKE2 Cluster host. The RKE2 Cluster will translate ansible.cyberstrawberry.net to the AWX web-service container(s) automatically. SSL certificates are not covered in this documentation, but suffice to say, the can be configured on another reverse proxy such as Traefik or via Cert-Manager / JetStack. The process of setting this up goes outside the scope of this document.
- AWX WebUI: https://ansible.cyberstrawberry.net
Retrieving the Auto-Generated Admin Password
AWX will generate its own secure password the first time you set up AWX. This password is stored as a secret in Kubernetes. You can navigate to the WebUI of Rancher in the RKE2 Cluster as long as you have a DNS record matching the hostname you assigned to Rancher the first time you signed in.
- Rancher WebUI: https://awx-cluster.cyberstrawberry.net
- Alternatively, you can try running the following command to pull the admin password / secret automatically
kubectl get secret awx-admin-password -o jsonpath="{.data.password}" | base64 --decode ; echo
Troubleshooting
You may wish to want to track the deployment process to verify that it is actually doing something. There are a few Kubernetes commands that can assist with this listed below.
Show the container deployment progress for AWX
kubectl get pods -n awx
AWX-Manager Deployment Logs
You may want to track the internal logs of the awx-manager container which is responsible for the majority of the automated deployment of AWX. You can do so by running the command below.
kubectl logs -n awx awx-operator-controller-manager-6c58d59d97-qj2n2 -c awx-manager
:::note
The -6c58d59d97-qj2n2 noted at the end of the Kubernetes "Pod" mentioned in the command above is randomized. You will need to change it based on the name shown when running the kubectl get pods -n awx command.
:::